SEALSQ to Showcase Post‑Quantum Security Chips at Embedded World 2026: Making Hardware Root of Trust Deployable
SEALSQ plans to highlight quantum‑resistant chips and device-identity tooling, signaling that post‑quantum migration is moving from software to hardware supply chains.
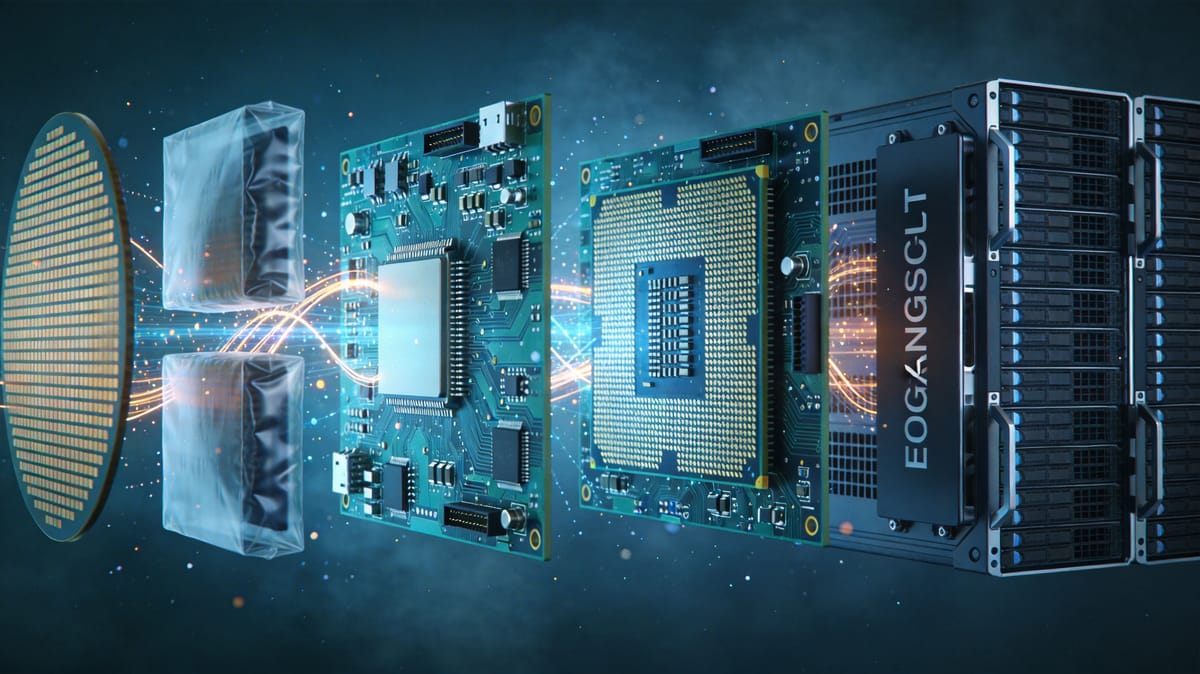
Post‑quantum cryptography is increasingly “solved” at the standards layer, but the harder part is turning new algorithms into something organizations can procure at scale, operate reliably, and audit over long device lifecycles. SEALSQ’s announcement that it will showcase quantum‑resistant chips and related capabilities at Embedded World 2026 is a useful marker: the post‑quantum transition is shifting from protocol discussions toward hardware Root of Trust productization.
The headline is not a single benchmark but an end‑to‑end device identity stack. SEALSQ says it will feature the QVault TPM and the QS7001 platform. The QVault TPM is positioned as a standalone security chip focused on hardware‑isolated key storage, secure boot, device attestation, and integrity verification for industrial gateways, embedded PCs, medical devices, and network equipment. The QS7001 is described as a secure RISC‑V microcontroller platform with an embedded hardware Root of Trust and native post‑quantum algorithms aligned with NIST‑selected standards, targeting industrial control, smart energy, automotive ECUs, robotics, and secure IoT edge deployments.
Why does it matter that post‑quantum capabilities are landing in TPM‑class components and secure microcontrollers. Many enterprises are less worried about whether PQC algorithms are “strong enough” and more worried about whether migration will undermine availability, maintainability, and compliance. In production devices, key management is never just compute and store. It includes key generation, secure storage, update and revocation, lifecycle governance, and binding keys to the boot chain and firmware authenticity. TPMs and hardware Roots of Trust provide a verifiable boundary that makes those lifecycle properties more deterministic.
This becomes critical because post‑quantum migration has a long‑tail reality. Cloud services can upgrade TLS and certificate policies comparatively quickly. Industrial, medical, energy, and automotive devices often have lifetimes measured in years or decades. Quantum risk is also not only a future problem: the “harvest now, decrypt later” model means data and firmware artifacts intercepted today could be compromised when large‑scale quantum capabilities arrive. For long‑lived device fleets, pushing PQC into hardware is a pragmatic way to reduce long‑term exposure.
SEALSQ’s framing also emphasizes PKI and trust services, not only chips. It highlights hardware‑anchored device identities, zero‑touch provisioning, certificate lifecycle management, continuous attestation, and secure OTA updates, with references to integration paths across common device cloud ecosystems. In deployment terms, the biggest obstacle is usually fleet operations rather than single‑device enablement. Treating PQC readiness as an operational capability—rather than a one‑off integration project—can lower friction for adopters.
Another notable aspect is the presence of IC’Alps, SEALSQ’s ASIC design services subsidiary. Putting product and design services in the same story reflects an important industry truth: not every OEM will adopt an off‑the‑shelf security chip. In domains like implantable medical devices, industrial control, and automotive electronics, constraints around power, area, cost, and certification often push teams toward custom SoCs with embedded security subsystems. In that scenario, “post‑quantum ready” may mean packaging cryptography and Root of Trust as reusable IP blocks and supply‑chain processes that can be integrated into the next platform generation.
From a supply‑chain perspective, post‑quantum hardware is not just a new SKU. Once Root of Trust becomes the trust anchor, manufacturing and provisioning need to support stronger controls: secure key injection, traceability, hardened testing flows, and clear auditability. PQC in hardware expands security responsibilities beyond software teams into silicon design, production, and operations.
SEALSQ also mentions a proof‑of‑concept collaboration with Lattice Semiconductor to demonstrate a TPM‑FPGA architecture. That direction is notable because FPGAs are widely deployed at the edge and can evolve after manufacturing via reprogramming. If the Root of Trust and programmable logic are tied together cleanly, new security capabilities could be pushed deeper into existing device classes without full redesign cycles.
Overall, announcements like this are more indicative of industry phase change than another algorithm paper. The next stage of post‑quantum readiness will be defined by purchasable components, reusable IP, operational certificate systems, and delivery chains that can pass compliance audits. The vendors who make that “boring” infrastructure deployable are likely to own key entry points in the embedded and industrial IoT security upgrade cycle.
Source: GlobeNewswire, The Manila Times